The most powerful way to find, monitor, and protect sensitive data at scale.
Rapidly reduce risk, detect abnormal behavior, and prove compliance with the all-in-one data security platform that won’t slow you down.




The all-in-one data security platform that won’t slow you down.
Varonis has developed a proven, efficient methodology for organizations to monitor, protect, and manage their data. Varonis data-centric approach reduces risk, increases efficiency and helps achieve compliance with data-centric regulations like PCI, HIPAA, and GDPR.
Know where your sensitive data lives.
Ensure only the right people have access.
Detect and stop malware and insider threats.
Sustain a secure state without manual effort.
A platform, a team, and a plan
that gives you every possible advantage
An Integrated Platform
Classification, access governance and behavioral analytics combine to lock down data, stop threats, and take the pain out of compliance.
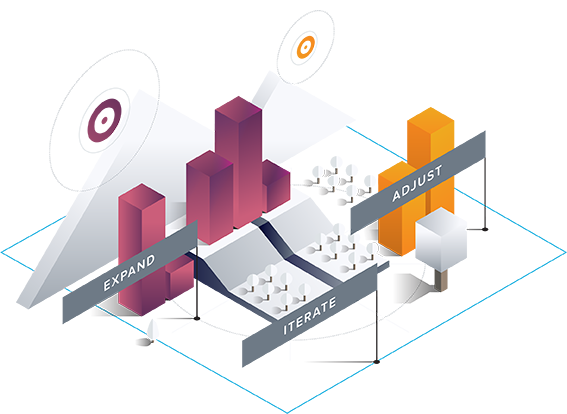
A Proven Plan to Make it Work
We bring you a proven methodology to monitor, protect, and manage your data informed by thousands of successful rollouts.
A Team Who Keeps You Miles Ahead
Hundreds of elite security pros build advanced threat models, update policies, and assist with incidents, freeing you to focus on other priorities.
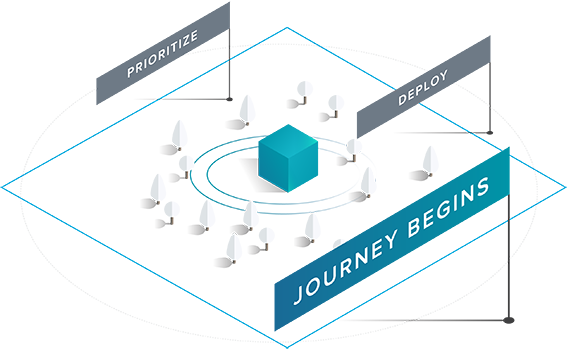
Deploy
- Deploy Varonis
- Discover privileged accounts
- Classify sensitive data
- Baseline activity
- Prioritize risk
Benefits
- Visibility into data risk profile
- Increased activity tracking
Operationalize
- Enable alerts and automate response
- Connect to SIEM
- Create and test incident response plans
- Operationalize reporting
- Apply classification labels
- Index for compliance
Benefits
- Incident response plans and automation reduce risk of data theft and loss
- Staff becomes more operationally efficient with day to day tasks
Fix
- Remediate exposed sensitive data
- Eliminate remaining global access groups
- Eliminate AD artifacts
- Quarantine sensitive data
- Archive/delete stale data
Benefits
- Significant risk reduction
- Defensible position with respect to compliance
- More efficient usage of storage
- Reduced complexity increases operational efficiency
Transform
- Identify and assign data owners
- Simplify permissions structure
- Enable data-driven reporting
Benefits
- Dramatic increase in operational efficiencies
- Better service for end users (faster access to data)
- Reduced complexity and risk
Automate
- Automate authorization workflow via data owners
- Automate periodic entitlement reviews
- Automate disposition, quarantining, policy enforcement
Benefits
- Reduced risk as policy deviations are corrected automatically and least privilege model is maintained
- Increased operational efficiency
- Evidence of process adherence for compliance
Improve
- Regularly review risks, alerts and processes to ensure continuous improvement
Benefits
- Ongoing improvements in risk reduction and operational efficiency