In recent weeks the Ukrainian Army and some major banks were subject to DDoS attacks. These attacks aim to severely impair and disrupt critical business services and they can happen at any time, not only during war.
“Cyber-Attacks” are attempts, whether conducted by individuals or groups, to compromise a computer system, network, or device with the aim of doing damage by stealing data and causing major damage to computer networks. This can be done regardless of where your computer is physically located. Attacks can be directed at governments, businesses, or individuals. A cyberattack can paralyze computer systems, causing a business to lose money when its website is unavailable, or for a government service to be interrupted. Moreover, a large amount of sensitive data could be stolen, which could negatively affect individuals on a financial or personal level.
A Cybercriminal can have various motivations for launching an attack such as personal or financial benefit. These hackers may act for social or political causes or may be sent by governments to steal information about enemies or terrorists.
The Director of National Intelligence expressed concern about potential threats affecting the U.S. There are a few countries and criminal groups in cyberspace that pose a threat to the US government and businesses. Russia is a major concern, but there were also other countries flagged as risks to U.S. cybersecurity. Hackers associated with the Chinese government represent the “most active” threat, the report states. “China almost certainly is capable of launching cyberattacks that would disrupt critical infrastructure services within the United States.”
Israeli National Cyber Directorate confirmed that a DDoS attack knocked numerous Israeli government websites on March 14, 2022. The Cyber Attack confirms that there is an increase in DDoS attacks targeting government websites.
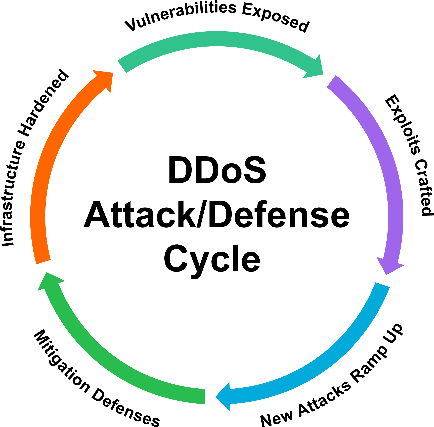
The challenge for organisations is that DDoS attacks have become increasingly sophisticated and multi-vector in nature. DDoS attacks can saturate systems, the headline grabbers are the large attacks. However traditional DDoS techniques don’t effectively stop the growth in the smaller shorter duration attacks.
Is there a way to prevent it from happening in my business?
Choosing a provider that best protects you from DDoS attacks is the first step and one that can provide instant mitigation at the edge of the network and simultaneously delivering instant reporting and analytics..
Corero Network Security is dedicated to improving the security and availability of the Internet, through the development of innovative DDoS mitigation solutions.
Invest in real-time, always-on DDoS protection! Corero Network Security is a global leader in real-time, high-performance, automatic DDoS defense solutions. Service and Hosting providers, alongside digital enterprises across the globe rely on Corero’s award winning cybersecurity technology to eliminate the threat of Distributed Denial of Service (DDoS) to their digital environment.
DDoS attacks are growing in frequency and have become much harder to detect and mitigate as they are increasing in frequency and sophistication. In today’s online world, even seconds of downtime can cost an organization thousands of dollars and destroy brand reputation. The only way to ensure business continuity when faced with the growing threat of attacks, is by investing in a real-time, always-on DDoS detection and mitigation solution offered by Corero Network Security.
Without proper protection in place, the chance of your organization being impacted is now higher than ever before. With proper protection the chance of any downtime greatly decreases.
With Corero’s DDoS protection you are safe with A leader in real-time, high-performance, automatic DDoS attack protection distributed by Multipoint Group, a leading distributer off IT security and internet technology solutions, providing channel partners in EMEA with reliable, supported solutions from world-leading hardware and software vendors.
For more information, visit https://multipoint.eu.com/corero/
and follow us on LinkedIn







