Perimeter81 Webinar
https://youtu.be/UCJs34jVolMSometimes it isn’t enough to “set and forget” – you need an in-depth view of your networks and policies. The monitoring dashboard from Perimeter81, gives you a minute-to-minute view of…
https://youtu.be/UCJs34jVolMSometimes it isn’t enough to “set and forget” – you need an in-depth view of your networks and policies. The monitoring dashboard from Perimeter81, gives you a minute-to-minute view of…
Gartner® Report How to Select the Right ZTNA Offering Choosing a ZTNA solution that’s right for your organization’s network security Download The Report Get Gartner® insights into choosing the right…
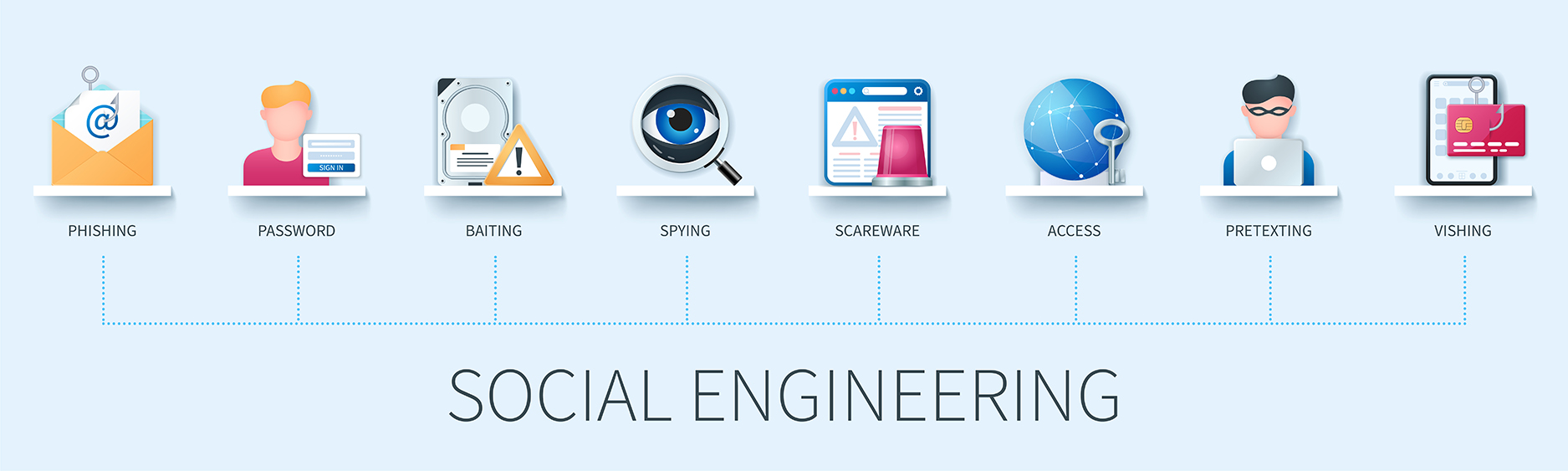
What are Social Engineering Attacks?Social Engineering is an act of manipulating people to expose confidential or sensitive information.This can be done by telephone, email, or face-to-face contact. It is the…
20 CRITICAL SECURITY CONTROLS Developed and periodically updated by a global community of experts, the 20 controls are “the most effective and specific set of technical measures available to detect,…
Use these 20 CRITICAL SECURITY CONTROLS Developed and periodically updated by a global community of experts, the 20 controls are “the most effective and specific set of technical measures available…
Protect your company against data loss and insider threat with Safetica. During a guided tour, we help you understand how is Safetica a good fit to your data security needs.Identify…
Phishing attacks and account takeovers are on the rise, yet not all types of multi-factor authentication (MFA) are up to the task of preventing modern phishing attacks. Similar to usernames…
Your least privilege cybersecurity journey begins here. With more than 80 percent of breaches involving the compromise of IT and business user credentials (IDs and passwords), organizations are limiting privileged access to…
https://youtu.be/mHq1J2r6rSgYour security challenges grow faster than your team. That’s why you need security testing automation built into every step of your SDLC.- Automate security tasks and save your team hundreds…
Why an investment in PAM is your best bet to combat cyber attacks https://www.youtube.com/watch?v=gH7boH02jMgCloud Transformation is Increasing Ransomware Risk according to the latest Cybersecurity Research.What will you learn?- The latest…